Hacker Uploaded “Sensitive” Documents From Royal Malaysian Navy on The Dark Web
 Thirsty for JUICE content? Quench your cravings on our Instagram, TikTok and WhatsApp
Thirsty for JUICE content? Quench your cravings on our Instagram, TikTok and WhatsApp

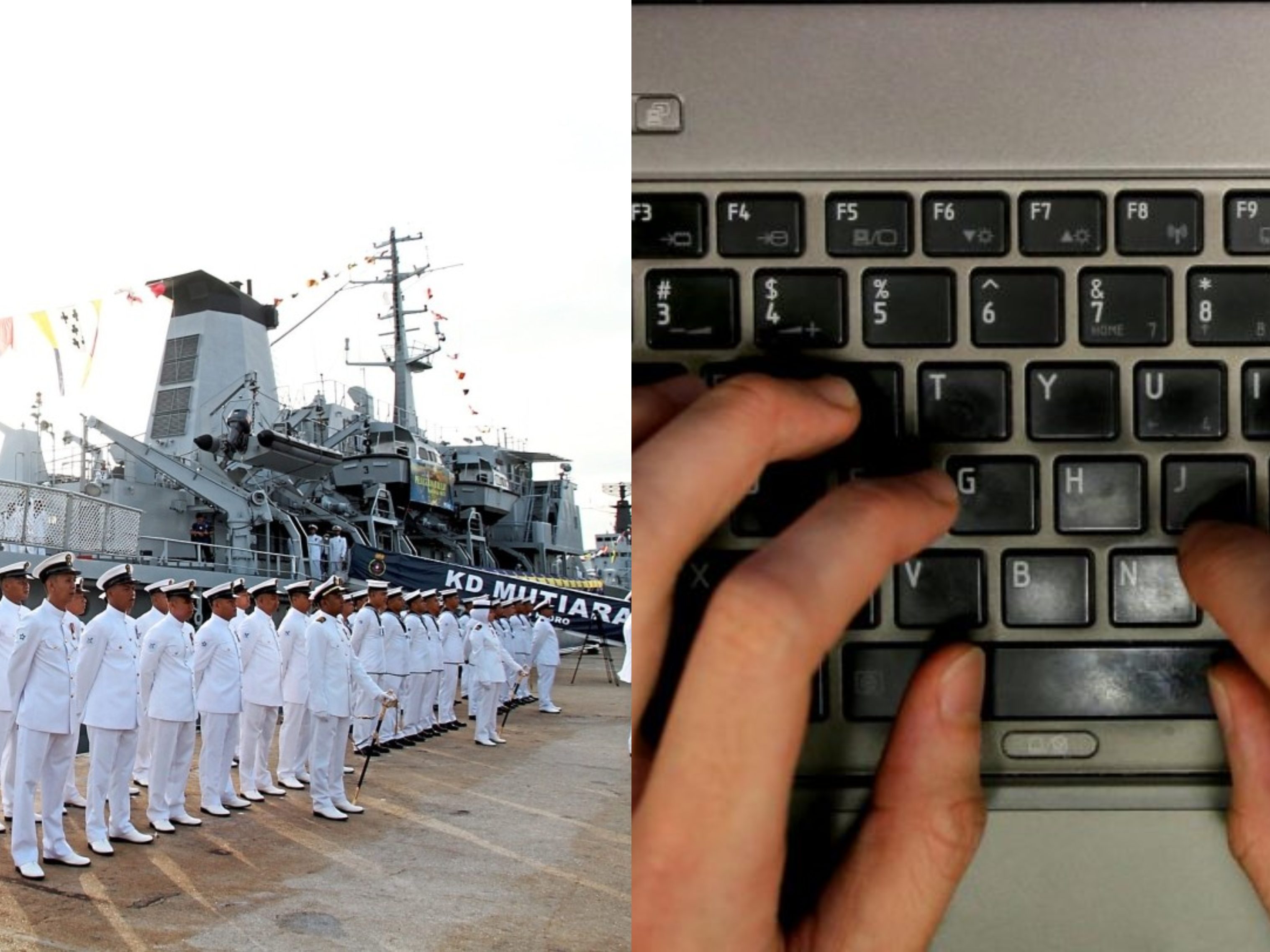
According to SG’s The Straits Times, around 70 documents from the Royal Malaysian Navy (RMN) were leaked and have ended up on a Dark Web portal, last month.
The uploaded information was understood to be from several sources that hacked into military personnel’s email accounts. However, it was not known if the uploader’s intention was to sell or share such data.
The documents are among a host of stolen military-related information from various countries and defence contractors which includes documents belonging to the US army and air force, as well as the Nigerian navy, European and Indian defence contractors.

ST said the uploaded documents included information on the number of troops at some Malaysian naval and army bases last year during a holiday, requirements for naval examination and senior and junior officials of the Malaysian navy who had been charged with corruption, taking drugs and being absent without leave.
The documents also included a US diplomatic letter last July that detailed a US Navy ship’s radar equipment and frequencies used when it asked for the ship to be docked at a port in Sabah in August last year.
Noting that it has alerted the RMN about the leaked data, a spokesman replied that “The RMN has no comment on the issue”.

The report cited security and intelligence experts who said that such data breaches, while apparently shocking, were not uncommon. Cyber Intelligence House CEO Mikko Niemela said such documents are often seen in “specialised” markets or forums on the Dark Web and usually paid for in bitcoins which ensures the anonymity of buyers and sellers.
“The reason why they are often seen in ‘specialised’ markets or forums (such as the Dark Web) is because it makes it easier for the potential clientele to access that information,” he was quoted as saying.
In case you didn’t know, the dark web is a decentralized network of internet sites that try to make users as anonymous as possible by routing all their communications through multiple servers and encrypting it at every step.
Among others, hacked and stolen information are usually sold and traded for cryptocurrency anonymously.


 Get Audio+
Get Audio+ Hot FM
Hot FM Kool 101
Kool 101 Eight FM
Eight FM Fly FM
Fly FM Molek FM
Molek FM

